Building
Trustworthy
AI Agents
A structured guide to designing AI agents that are safe, transparent, controllable, and aligned with human values — with real-world examples and visual flows.
Why Trust is the
Central Challenge
AI agents are no longer just chatbots answering questions — they browse the web, write and execute code, send emails, manage files, and make decisions with real-world consequences. The higher the autonomy, the higher the stakes.
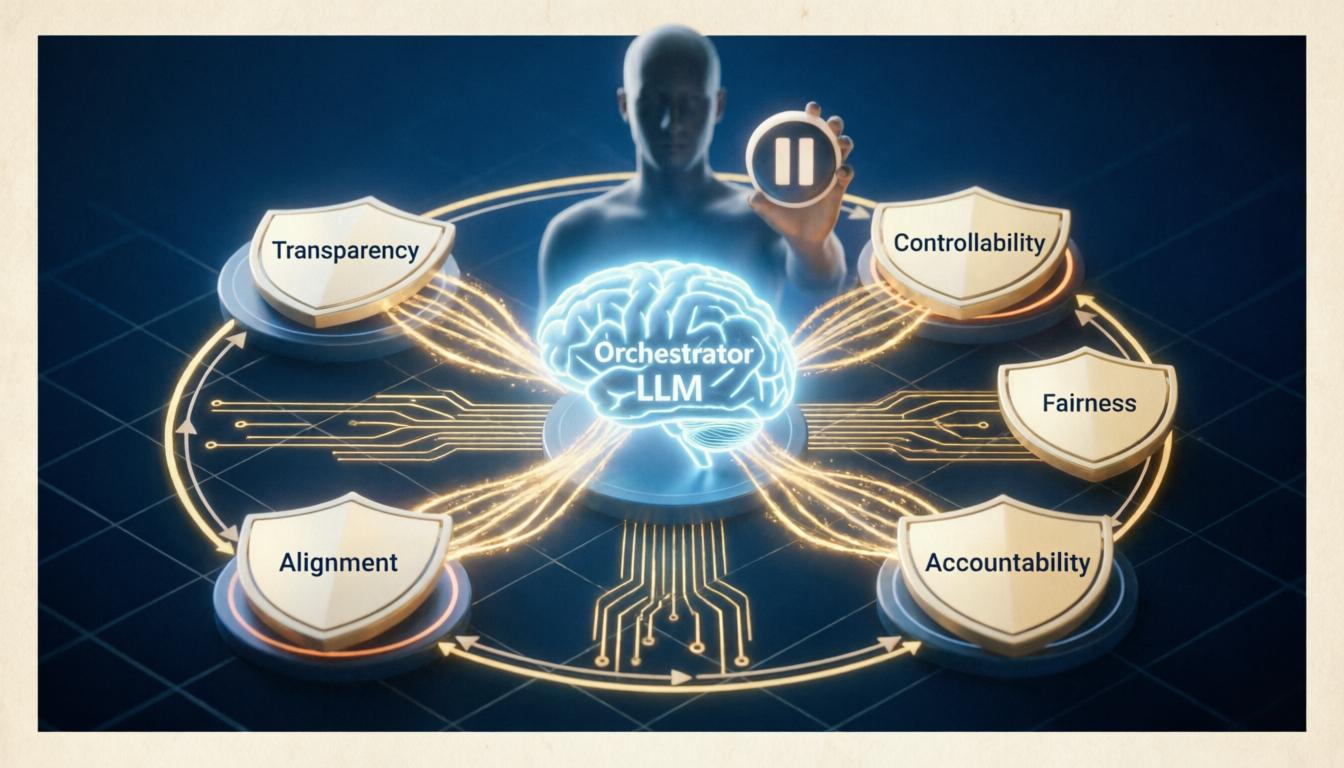
Trust in AI agents is not a single property — it is a composite of transparency, safety, reliability, fairness, and meaningful human oversight. Lose any one of these, and the entire system becomes fragile.
The agent explains its reasoning, cites sources, and makes its decision process visible to users and auditors.
The agent avoids harmful actions, refuses malicious instructions, and errs toward caution in ambiguous situations.
Humans can pause, override, correct, or shut down the agent at any point without friction or resistance.
The agent treats all users and groups equitably, without bias in its recommendations or actions.
Every action is logged, attributable, and reviewable. There is always a clear chain of responsibility.
The agent reliably pursues the user’s actual intent, not just the literal instruction — including long-term wellbeing.
The Trustworthy
Agent Decision Flow
Every action an AI agent takes should pass through a principled pipeline — from receiving a task to validating safety before execution, with human checkpoints woven throughout.
Built-In Guard Rails
Guard rails are the enforcement layer of trust — they act as automatic checks before and after every consequential action the agent takes.
The agent maintains a clear boundary of actions it will never take — bypassing authentication, deleting data without confirmation, impersonating humans, or violating user privacy — regardless of how the instruction is framed.
High-stakes decisions — sending emails, making purchases, modifying databases — require explicit human confirmation before execution. The agent surfaces the action in clear language before proceeding.
Every tool call, retrieval, decision branch, and output is logged with timestamps and reasons. The log is write-once, tamper-evident, and reviewable by authorized parties at any time.
Any operator or user can pause or terminate the agent mid-task. The agent saves its current state, reports what it has done, and hands off cleanly — never leaving systems in a broken intermediate state.
Trustworthy AI in Practice
Across industries, trustworthy AI agents apply these principles in domain-specific ways — always balancing autonomy with oversight.
Scenario
Agent suggests treatment options for a patient based on EHR, drug interactions, and clinical guidelines.
Trust Mechanisms
Cites sources Flags uncertainty Clinician approval required HIPAA audit log
Key Risk Handled
Drug contraindications flagged automatically; any suggestion with >15% uncertainty escalates to physician review.
Human Checkpoint
No prescription or treatment plan is finalized without a licensed clinician’s digital sign-off.
Scenario
Agent executes trades, rebalances portfolios, and generates compliance reports based on client strategy.
Trust Mechanisms
Explainable rationale Position size limits Kill switch Regulatory audit trail
Key Risk Handled
Hard-coded position limits prevent runaway trades; all large orders require human confirmation above threshold.
Human Checkpoint
Any single trade exceeding 2% of portfolio value pauses for portfolio manager approval before execution.
Scenario
Agent reviews 200-page contracts, flags risky clauses, and suggests redlines aligned with company policy.
Trust Mechanisms
Clause-level citations Confidence scores Attorney review gate Version history
Key Risk Handled
Agent never signs or sends documents. All suggested changes are tracked diffs requiring attorney acceptance.
Human Checkpoint
Final contract execution requires authorized attorney’s cryptographic signature — never the agent’s.
Scenario
Agent monitors factory floor sensors, detects anomalies, and recommends or takes corrective actions.
Trust Mechanisms
Sensor data provenance Safe-state defaults Manual override always active ISO compliance log
Key Risk Handled
Safety-critical actuators (emergency stops, pressure valves) can only be commanded by the agent within pre-defined safe ranges.
Human Checkpoint
Plant supervisor receives real-time dashboard of all agent actions with one-click override for any command.
Scenario
Agent adapts curriculum, generates exercises, and tracks student progress across subjects over time.
Trust Mechanisms
Learning rationale shown Age-appropriate filters Parent/teacher visibility COPPA compliance
Key Risk Handled
Strict content filters for minors; any topic outside approved curriculum triggers automatic teacher notification.
Human Checkpoint
Weekly progress reports go to teachers and parents; curriculum changes require educator approval for minors.
Scenario
Agent monitors network traffic, identifies intrusion attempts, and can isolate affected systems automatically.
Trust Mechanisms
Evidence chain logged Blast radius limits SOC team notified Forensic audit trail
Key Risk Handled
Agent can only isolate — never delete — systems autonomously. Destructive actions require CISO authorization.
Human Checkpoint
SOC analysts receive real-time alerts for every isolation event with full context and one-click rollback.
What to Build Into
Every Agent
These four principles should be non-negotiable requirements in the architecture of any AI agent deployed in real-world settings.
Request only necessary permissions. Store only required data. Prefer reversible actions over irreversible ones.
Volunteer uncertainty. Surface conflicts of information. Never hide limitations or failures from users.
When unsure, do less. Partial results with clear caveats are better than confident wrong answers.
Trust must be earned over time. Monitor, measure, and recalibrate the agent’s autonomy based on track record.